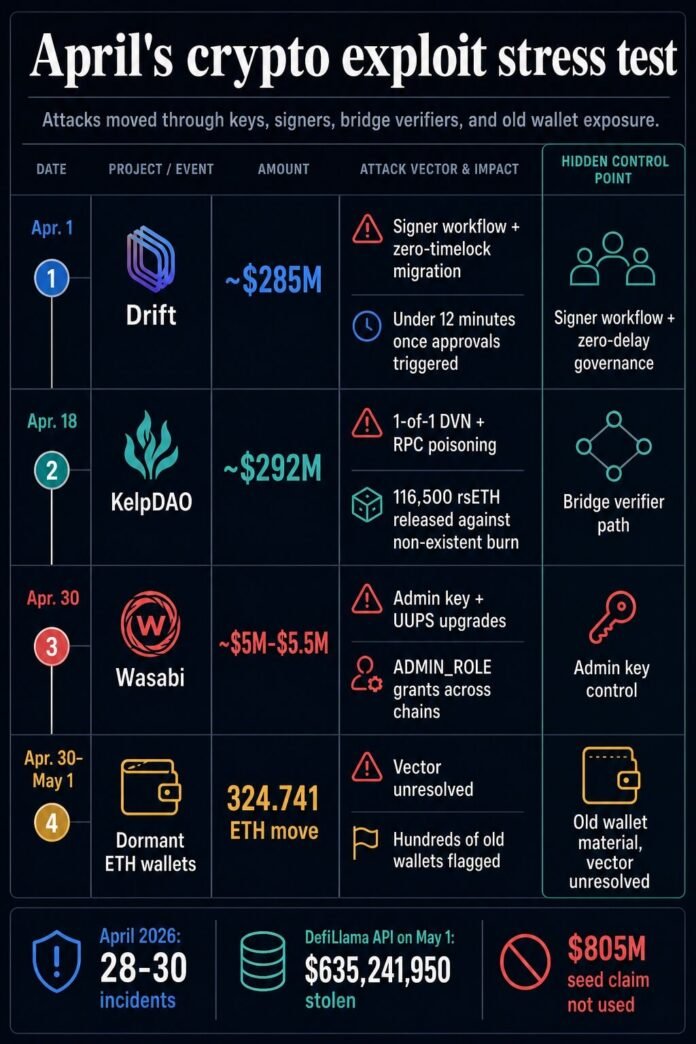
Hundreds of Ethereum wallets that had sat untouched for years were drained into the same tagged address, turning old key exposure into this week’s sharpest crypto security warning.
On Apr. 30, WazzCrypto flagged the incident affecting mainnet wallets on X, and their warning spread quickly because the affected accounts did not appear to be freshly baited hot wallets. They were old wallets with quiet histories, some tied to assets and tooling from an earlier Ethereum era.
Over 260 ETH, roughly $600,000, was drained from hundreds of dormant wallets. More than 500 wallets appear to be affected, with losses totaling roughly $800,000, and many wallets have been idle for four to eight years. The related Etherscan address is labeledFake_Phishing2831105, and shows 596 transactions, and records a 324.741 ETH movement to THORChain Router v4.1.1 around the Apr. 30 window.
The constant across them is more important for now: long-idle wallets have been moved to a common destination, while the compromise path remains unresolved.
That unresolved vector makes the drain the strongest warning this week, following a surge in DeFi hacks. Protocol exploits usually give investigators a contract, a function call, or a privileged transaction to inspect.
Here, the central question sits at the wallet layer. Did someone obtain old seed phrases, crack weakly generated keys, use leaked private-key material, abuse a tool that once handled keys, or exploit another path that has yet to surface?
Public discussion has produced theories including weak entropy in legacy wallet tools, compromised mnemonics, trading-bot key handling, and LastPass-era seed storage. One affected user personally raised the LastPass theory.
The practical advice for users is limited but urgent. Idleness does not mitigate private-key risk. A wallet with value depends on the full history of the key, the seed phrase, the device that generated it, the software that touched it, and every place that secret may have been stored.
For users, the response is probably to inventory high-value old wallets, move funds only after setting up fresh key material through trusted hardware or modern wallet software, and avoid entering old seeds into checkers, scripts, or unfamiliar recovery tools. Revoking approvals helps for protocol exposure, including Wasabi’s user warning, but a direct wallet drain points first to key security rather than token approvals.
April widened the control surface
The wallet cluster landed amid April’s crypto exploit tally, which was already elevated. DefiLlama-linked reporting put April at roughly 28 to 30 incidents and more than $625 million in stolen funds. As of May 1, the live DefiLlama API showed 28 April incidents totaling $635,241,950.
A May 1 market thread captured the pressure point: this week’s wallet drains, Wasabi Protocol’s admin-key exploit, and April’s larger DeFi losses all hit control surfaces that ordinary users rarely inspect. The link across the month is architectural rather than attributional.
Admin paths became attack paths
Wasabi Protocol supplies the clearest recent protocol example. The Apr. 30 exploit reportedly drained roughly $4.5 million to $5.5 million after an attacker gained deployer/admin authority, granted ADMIN_ROLE to attacker-controlled contracts, and used UUPS proxy upgrades to drain vaults and pools across Ethereum, Base, and Blast. Early security alerts flagged the admin-upgrade pattern as the attack unfolded.
The reported mechanics put key management at the center of the incident. Upgradeability can be normal maintenance infrastructure. Concentrated upgrade authority turns that maintenance path into a high-value target. If one deployer or privileged account can change implementation logic across chains, the boundary around an audited contract can vanish once that authority is compromised.
That is the user-facing problem hidden inside many DeFi interfaces. A protocol can present open contracts, public front ends, and decentralization language while critical upgrade power still sits in a small set of operational keys.
Signers and verifiers carried the largest losses
Drift pushed the same control problem into signer workflow. Chainalysis described social engineering, durable nonce transactions, fake collateral, oracle manipulation, and a zero-timelock 2-of-5 Security Council migration. Blockaid put the loss around $285 million and argued that transaction simulation and stricter co-signer policies could have changed the outcome.
The Drift case matters here because the path did not depend on a simple public-function bug. It depended on a workflow where valid signatures and fast governance machinery could be turned toward a hostile migration. A signer process became the control surface.
KelpDAO moved the stress test into cross-chain verification. The incident statement described a bridge configuration in which the rsETH route used LayerZero Labs as the sole DVN verifier. Forensic reviews described compromised RPC nodes and DDoS pressure feeding false data to a single-point verification path.
The result, according to Chainalysis, was 116,500 rsETH, worth roughly $292 million, released against a non-existent burn. The token contract could remain intact while the bridge accepted a false premise. That is why a verifier failure can become a market-structure problem once the bridged asset sits inside lending markets and liquidity pools.
AI belongs in the speed discussion
I think Project Glasswing deserves a special mention here for context, separate from causation. Anthropic says Claude Mythos Preview found thousands of high-severity software vulnerabilities and shows how AI can compress vulnerability discovery. That raises the bar for defenders, but the causal record in these crypto incidents points to keys, signers, admin powers, bridge verification, RPC dependencies, and unresolved wallet exposure.
The security implications are still serious. Faster discovery gives attackers and defenders more parallel surface to work through. It also makes old operational shortcuts more expensive because dormant secrets, privileged keys, and single-verifier paths can be tested faster than teams can manually review them.
The repair list is operational
The controls that follow from April sit above and around the codebase.
| Incident | Hidden control point | Failure mode | Practical control |
|---|---|---|---|
| Dormant Ethereum wallets | Old wallet material | Funds moved from long-idle wallets into a tagged address while the vector remains unresolved | Fresh key generation for valuable dormant funds, cautious migration, and no seed entry into unknown tools |
| Wasabi | Admin and upgrade authority | Privileged role grants and UUPS upgrades enabled vault and pool drains | Key rotation, stronger thresholds, bounded admin powers, timelocks, and independent monitoring of upgrade actions |
| Drift | Security Council signer workflow | Pre-signed durable nonce transactions and zero-delay governance enabled fast admin takeover | Higher thresholds, delay windows, transaction simulation, and policy-enforced co-signing |
| KelpDAO | Bridge verification path | RPC poisoning and a 1-of-1 DVN route allowed a false cross-chain message to pass | Multi-DVN verification, cross-chain invariant monitoring, and independent checks outside the same verifier path |
For protocols, the priority is to reduce the amount that any single authority can do at once. That means time locks on admin operations, stronger and more stable signer thresholds, monitored privileged-transaction queues, explicit limits on parameter changes, and co-signing systems that simulate transaction effects before humans approve them.
For bridges, the priority is independent verification and invariant checks. A cross-chain message should be tested against the economic fact it claims to represent. If rsETH leaves one side, the system should verify the corresponding state change on the other side before the destination side releases value. That monitoring needs to exist outside the same path that signs the message.
For users, the repair list is smaller. Move valuable old funds to fresh keys through a process you already trust. Separate that action from protocol-specific approval cleanup. Treat every claim about the wallet-drain root cause as provisional until forensic work identifies a common tool, storage path, or exposure source.
The next test
April proved that the average user’s security checklist is likely incomplete. Audits, public contracts, and decentralized interfaces can coexist with concentrated admin authority, weak signer procedures, brittle bridge verification, and old wallet secrets.
The next quarter will reward proof over decentralization language: constrained upgrade powers, visible timelocks, independent verifier paths, transaction simulation for privileged actions, disciplined access controls, and documented key rotation.
The dormant-wallet drains show the uncomfortable user-side version of the same problem. A system can look quiet while an old control failure waits in the background. April’s exploit wave exposed that layer above the code; the next phase will show which teams treat it as core security before funds move.